goodfet.nrf
Client
Usage: goodfet.nrf verb [objects]
goodfet.nrf info
goodfet.nrf test
goodfet.nrf regs
goodfet.nrf regbits
goodfet.nrf pyregs
goodfet.nrf tune aa|55,mac,r5,r6
Tunes to a configuration.
goodfet.nrf sniff
Sniffs packets by current config.
goodfet.nrf sniffob
Sniffs OpenBeacon traffic.
goodfet.nrf snifftp
Sniffs Turning Point Clicker traffic.
goodfet.nrf sniffsf
Sniffs SparkFun Dongle traffic.
goodfet.nrf sniffmskb
Sniffs Microsoft Keyboard traffic.
goodfet.nrf sniffmacs
Sniffs for MAC addresses on the present channel.
goodfet.nrf sniffprom [0xaa|0x55]
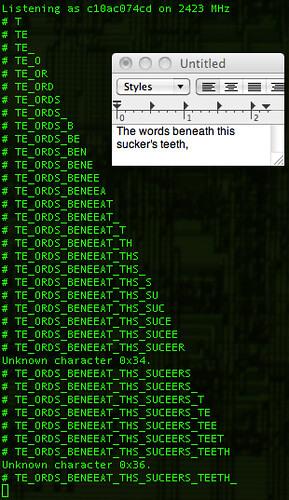
Sniffs promiscuously for a preamble of 0xAA or 0x55
goodfet.nrf autotune
Searches for a valid destination address.
goodfet.nrf carrier [freq]
Holds a carrier on [freq] Hz.
Pinout
| Name | Pin | Name | |
|---|---|---|---|
| MISO | 1 | 2 | Vcc |
| MOSI | 3 | 4 | Vcc |
| SS | 5 | 6 | |
| SCK | 7 | 8 | |
| GND | 9 | 10 | |
| CE | 11 | 12 | |
| 13 | 14 | ||
Examples
Turning Point Clicker
The Turning Point ResponseCardRF series of audience response devices can be sniffed using 'goodfet.nrf snifftp'. See Travis Goodspeed's article, Reversing an RF Clicker, for details of how the protocol was reverse engineered.
OpenBeacon
The OpenBeacon and OpenAMD projects use Nordic radios to track the positions of conference and museum attendees. These can be sniffed with 'goodfet.nrf sniffob', but packets will be encrypted with XXTEA by all deployments except the Next Hope, where cryptography was disabled to facilitate badge hacking.
Additionally, the NHB12 and NHB12B badges from the Next Hope can be flashed with the GoodFET firmware to run this application.
Sparkfun Fob
A mode also exists to sniff the example firmware of Sparkfun's WRL-08602 Nordic FOB by 'goodfet.nrf sniffsf'.
Microsoft 2.4GHz Keyboard
Many Microsoft wireless keyboards use their MAC address as an XOR key, allowing packets to be easily intercepted and deciphered. A sniffer for this protocol was first implemented in the KerKeriki V2.0 project, and the GoodFET is now able to sniff this traffic as well. For more details, see Promiscuity is the nRF24L01+'s Duty.